With millions of customers dependent on connectivity services, network outages or data breaches are not an option
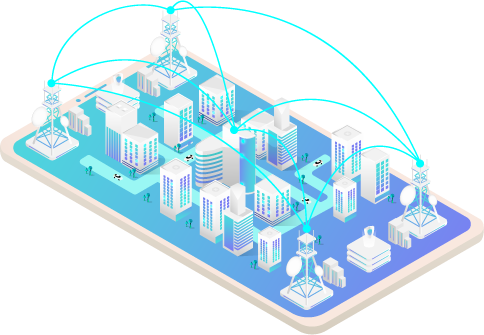
The telecommunications sector requires massive strength, reliability and scalability to assure the best customer service, as most of the time these companies rely on loyal customers that renew subscriptions and attest to service reliability. Telecommunications companies provide a broad range of services including data, Internet Protocol (IP), voice and wireless, managing simultaneously thousands of network equipment, including routers, LAN switches, firewalls, application appliances, wireless access points.

The business value that any telecommunication company offers includes innovative communications solutions delivered through a great end-to-end customer experience. Considering the matrix nature of this business, customer satisfaction is a must. With millions of customers dependent on dedicated communication services performing at their best efficiency, having network outages due to equipment failure is not an option.
If network outage prevention is very high on the list of challenges for IT telecommunication networks, crucial is also the risk of cyber threats causing data breaches or even network disruptions. Cybersecurity at the network level must be one of the top priorities for any telecommunication company. Not to forget that a data breach, in the best-case scenario, costs millions.
Monitoring telecommunication network infrastructures provides its own set of challenges:
- Achieving real-time network monitoring
- Detecting networking and operational issues before they cause downtime
- Preventing unplanned downtime due to equipment failure
- Remote access control
- Remote troubleshooting (intermittent) issues on hard to reach remote sites

Accessing the network traffic
Get a reliable, real-time overview of the network with physical and virtual TAPs placed at strategic points, and Bypass TAPs for an extra layer of security.
Managing & optimizing data flow
Build a visibility architecture with the help of Network Packet Brokers (NPB) to deliver actionable network data to monitoring and security tools.


Data capture and analysis
Leave no blind spots: get dedicated tools that enable monitoring on the spot, but also remotely, as well as back-in-time analysis. In particular, Deep Packet Inspection (DPI) allows drilling down into the metadata extracted from network packets to identify what protocols and applications are being used, who is using them, and from what devices. With this level of network traffic analysis, it is possible to detect the actual packets involved in client conversations and identify the root cause of technical or security issues.
